|
Site News | |
Our Black Friday section is now online! Click here to check it
out.
|
|

| |
Rooting the Sandman Doppler
Caution, work in progress, not responsible for damage, bricking, etc.
Don't pass this around until I delete this message. If you have issues feel
free to message me on Discord, I will try to help you through it and make
any necessary changes to the howto before I release it to a broad audience.
Step 1, setup the Sandman Doppler so it connects on your wifi network. Yes,
this can (probably) be bypassed with some manual configuration, but that is
currently outside the scope of this howto. That said...
Currently you will need either an iPhone that is on a version LOWER than 26
(I am currently on 18.7.1), or sideload the Sandman Doppler apk for Android
(can be downloaded
here).
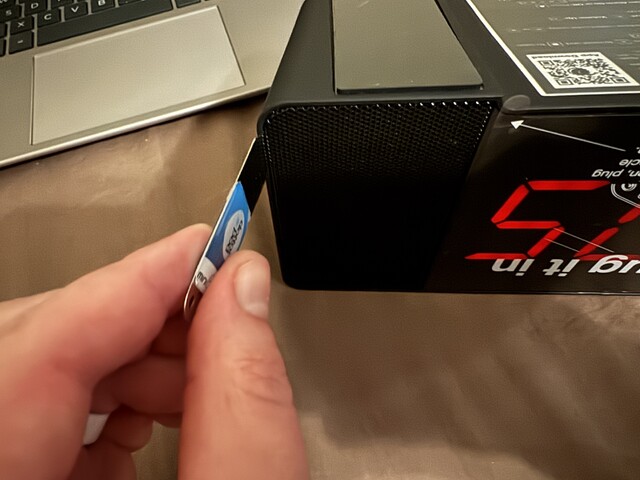
To connect to the Doppler, you will need a usb to serial device like this one:
www.amazon.com/dp/B00LZV1G6K.
If you've ever flashed a smart plug before, you likely have one already.
Once it is setup and gets an ip on your local network, flip it upside down
and gently pry off the left (to you) speaker grill, exposing the speaker and
the four screws holding it in.



Take out all four screws. Note, the screws are
different sizes, during
reassembly simply put back in the shorter screws...if they don't grab onto
any threads, then try the other screw holes instead. FYI with the Doppler
upside-down the "top" (bottom of the unit with
the label) has the short screws, and the "bottom" has the long screws.
Toward the front of the Doppler you will see the three pads we're interested
in, RXD TXD and GND.

Connect them using the cables on your usb to serial device
(note that TXD on the usb device goes to RXD on the Doppler; one device's transmit
goes to the other device's receive and vice versa). Start up a terminal and
connect to the usb device; in Linux I use minicom and the command would look
like:
minicom -b 115200 -D /dev/ttyUSB0
The "-b 115200" sets the baud rate (likely the default so probably not necessary)
and the "-D /dev/ttyUSB0" specifies what device to use (this may work as-is
for you, unless you have multiple usb to serial devices; check your distro's
documentation to see how to both install minicom and see what device your usb
to serial device is on).
Connect the TXD on the usb device to RXD on the Doppler (what is transmitted
from the usb device is received on the Doppler, and vice versa), RXD on the usb
device to TXD on the Doppler, and GND to GND. I use some electrical tape to
hold the ends together (disregard how sloppy it looks in the
non-existent photo, for another
device I needed four wires instead of three), carefully placed them in the
holes on the Doppler, fired up minicom, then hit enter to see the login prompt.
We can't actually login yet, this just lets us know our setup works (albeit
temporarily, feel free to solder to the Doppler if you want but it shouldn't
be necessary).
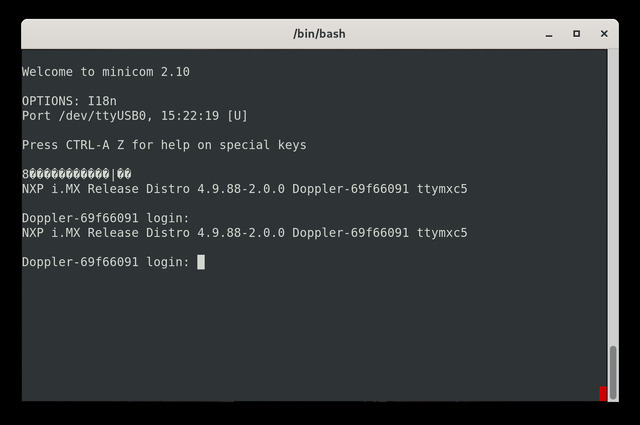
There is one setting in minicom we need to change, and that's to enable line
wrap. For me I pressed CTRL-A, then W (you can also CTRL-A and Z to bring up
the help menu, and there's an option called "lineWrap on/off" that says to press
W to toggle). If you see that lines aren't wrapping, toggle this.
Now that everything is setup and we've verified communication, we need to boot
the Doppler and interrupt its boot process so we can access uboot.
Unfortunately the Doppler detects if it's connected to serial on boot and
refuses to boot, so we need to be very quick. There is a green light that lights
up as soon as it starts booting, if it's not on you know it's paused. My
method is to make sure it's all connected, unplug then replug the Doppler from
power and
ensure the green light is off (thus meaning it's paused the boot process),
then on the usb device quickly disconnect and reconnect the GND wire while
pressing the enter key repeatedly, if you time it right you'll see something
like this on minicom:
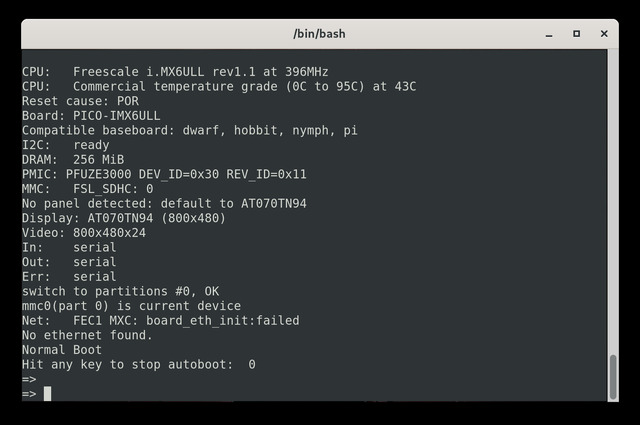
You may not get it the first time or five; until I learned the trick it worked
about one out of ten times, but eventually you should get the uboot screen.
Now, we need to edit the bootcmd. If you search how-tos for other devices
they will instruct you to edit bootargs, however the bootargs for the Doppler
are embedded in the bootcmd, so we edit that instead. We need to edit the
bootargs (which is in bootcmd) to have "init=/bin/sh" at the end. This is the
tricky part, because to see the whole line we need line wrap on (else it goes
way
off the screen and you'll never see it all), but we need to paste it back as
one line. So copy what "printenv bootcmd" gives you...
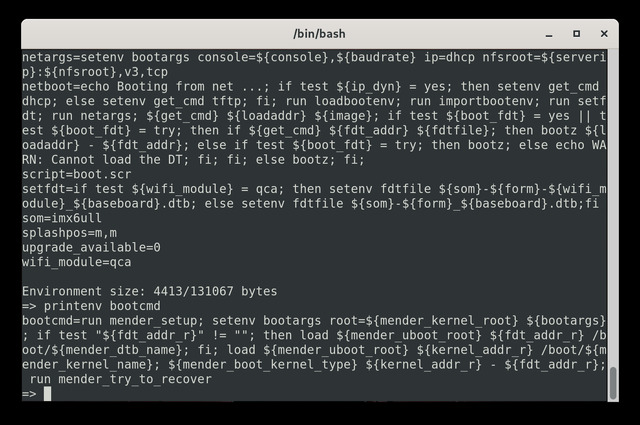
minus the "bootcmd=" at
the beginning, and put it in a text editor with word wrap OFF (so you know
that it's definitely all one line when you go to copy/paste it back). You also
need to surround it with SINGLE quotes (not double because those are parsed).
The end result should look something like this:
'run mender_setup; setenv bootargs root=${mender_kernel_root} ${bootargs} init=/bin/sh; if test "${fdt_addr_r}" != ""; then load ${mender_uboot_root} ${fdt_addr_r} /boot/${mender_dtb_name}; fi; load ${mender_uboot_root} ${kernel_addr_r} /boot/${mender_kernel_name}; ${mender_boot_kernel_type} ${kernel_addr_r} - ${fdt_addr_r}; run mender_try_to_recover'
We copy that (make sure it's one line), then carefully paste it in minicom
after typing "setenv bootcmd " (note the space after bootcmd), so the whole
command should look like (on one line):
setenv bootcmd 'run mender_setup; setenv bootargs root=${mender_kernel_root} ${bootargs} init=/bin/sh; if test "${fdt_addr_r}" != ""; then load ${mender_uboot_root} ${fdt_addr_r} /boot/${mender_dtb_name}; fi; load ${mender_uboot_root} ${kernel_addr_r} /boot/${mender_kernel_name}; ${mender_boot_kernel_type} ${kernel_addr_r} - ${fdt_addr_r}; run mender_try_to_recover'
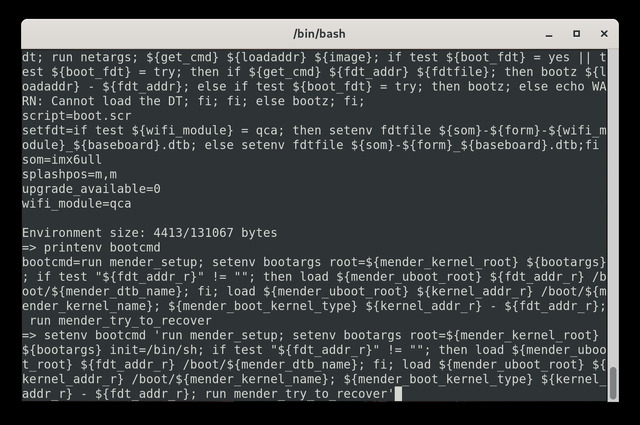
Press the enter key to save. Now type "boot" and enter, and cross your
fingers.
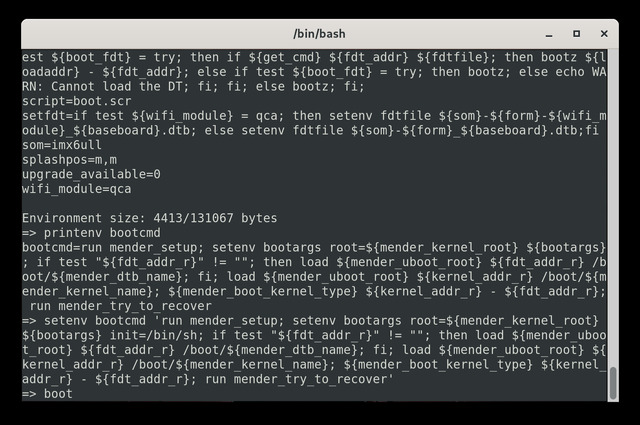
You do NOT need to mess with
the GND cable, as it's doing a warm boot. You should see it boot into a single
user shell as root.
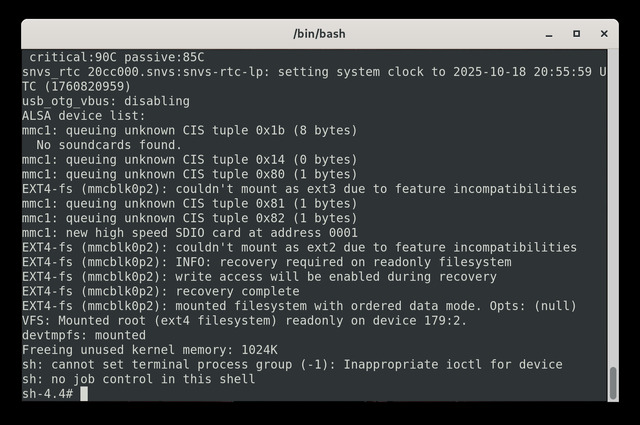
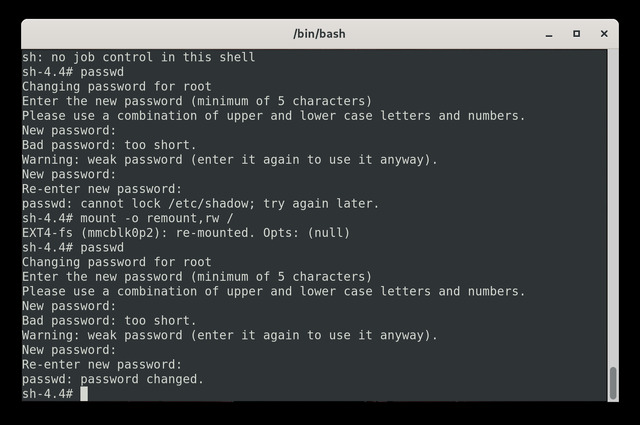
You need to remount / to be writable, so we issue this command:
mount -o remount,rw /
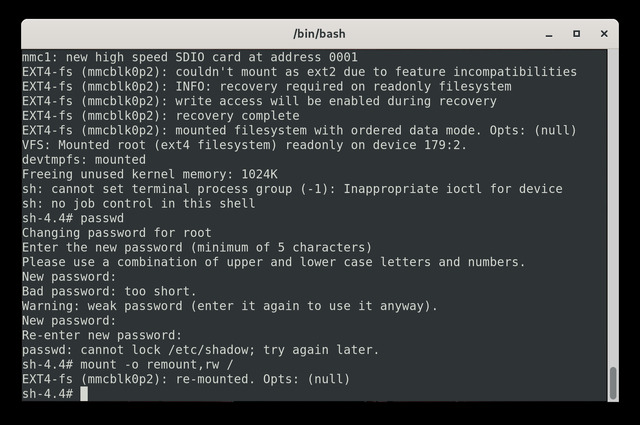
Now issue the passwd command and give it a password. Note
that for this howto I'm using 4545 as the root password, it
will complain that
it's insecure hence it makes you type it three times instead of the normal
two (after first it warns you, second it takes it seriously, then third is to
confirm; a more secure password would just ask you to confirm). Yes, I tried
to set the root password before mounting the partition rewritable, oops.
Now reboot by unplugging the Doppler, waiting a few seconds, then plugging it
back in. You will need to disconnect the usb serial device again, but you do
NOT need to worry about timing or pressing enter; we want it to boot normally.
It may automatically drop itself in the uboot prompt. If so, type "boot" and
enter, and you should see it boot normally.
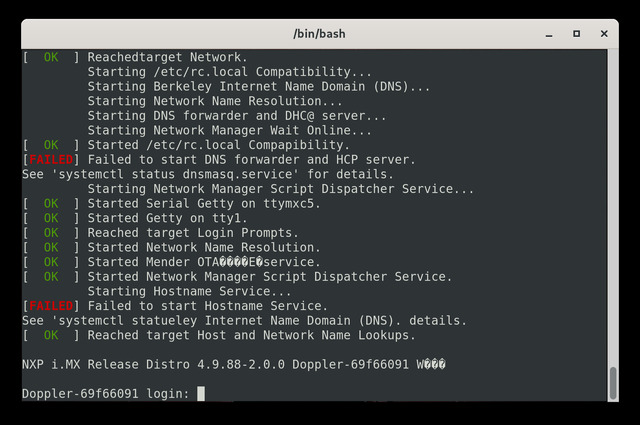
Another oddity, during boot it starts to display garbage characters while
starting the doppler process. This isn't an issue once we can login using
telnet or ssh, for the moment just wait a bit, once the Doppler is fully booted
(the time is displayed with no progress bar going back and forth) it should
be good to go, possibly a CTRL-Z and enter, that should bring you back to the
command line or login prompt.
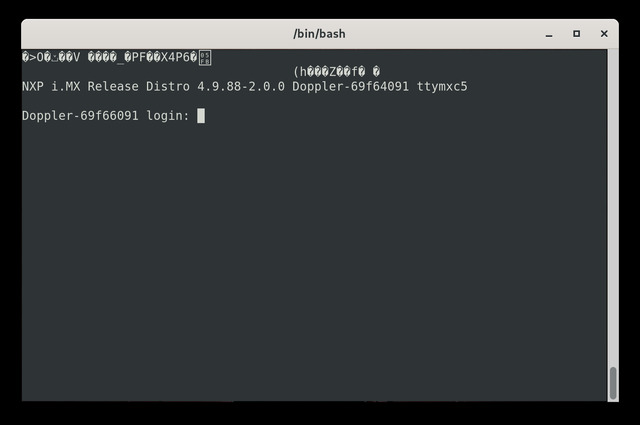
You will get sporadic garbage characters until
we can login via telnet, so let's get that done next.
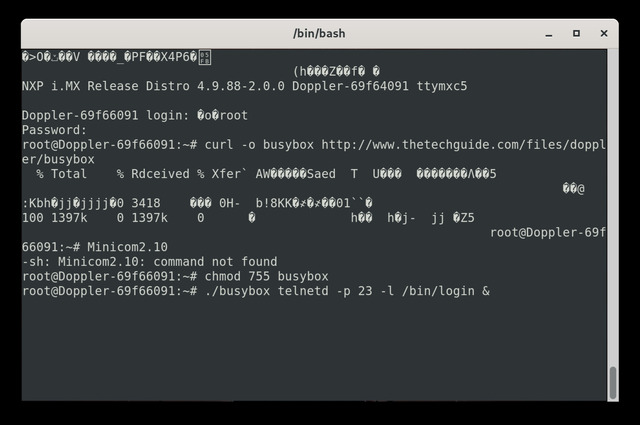
We need to download a more fully-featured busybox, luckily I've done the hard
work and you can download a custom version
here. Assuming
your Doppler can access the internet, we can download it directly to it using
this command:
curl -o busybox http://www.thetechguide.com/files/doppler/busybox
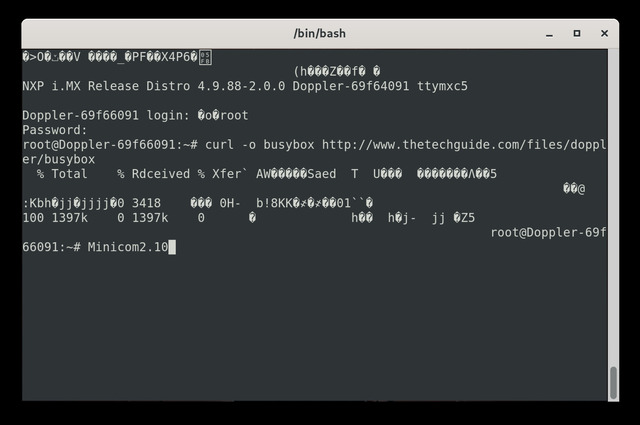
Again, garbage characters, but that's just cosmetic; the file should be
downloaded correctly. Press enter in the terminal program to clear out whatever
it thinks was typed in, and type this command:
chmod 755 busybox
Almost there! Now we start the telnet server manually using this command:
./busybox telnetd -p 23 -l /bin/login &
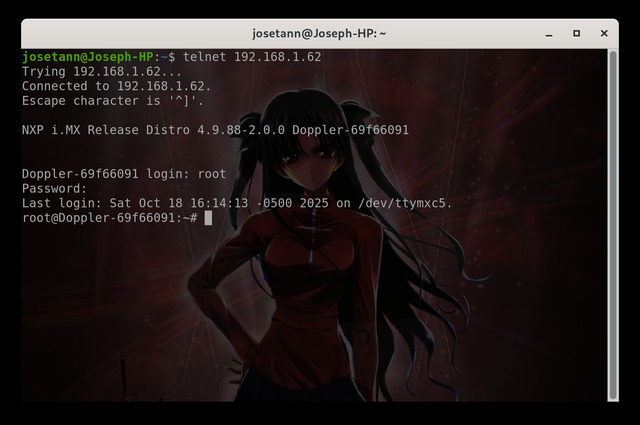
Ideally we can run "ip addr" to get the ip address, but I only get garbled
text, so try to find the ip address some other way, and telnet directly into
the Doppler. Login as root, password 4545
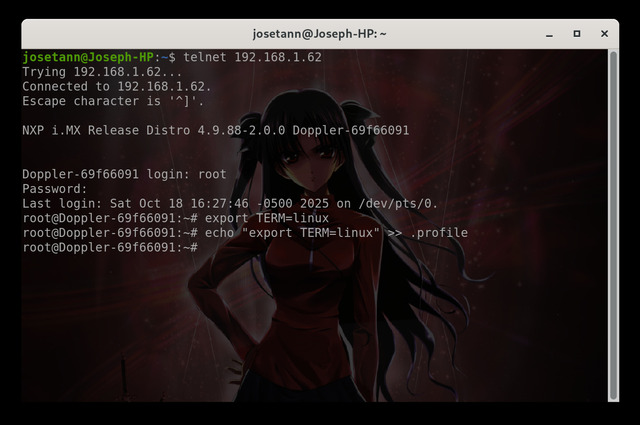
Now we are logged in, let's make this a bit more permanent. First, nano acts
a bit weird unless we export a variable, so type:
export TERM=linux
Let's also add it to our .profile.
echo 'export TERM=linux' >> .profile
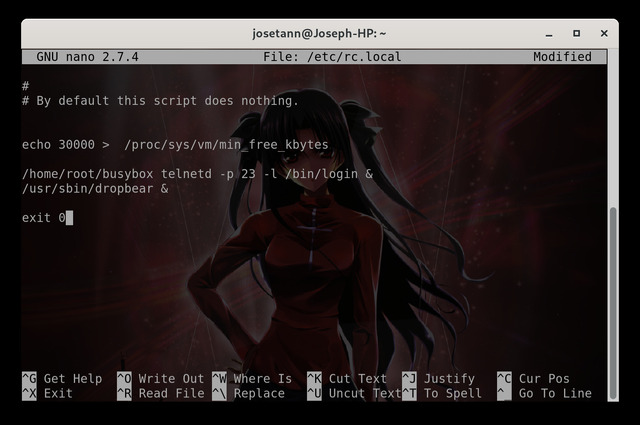
Now we can edit /etc/rc.local to automatically start our telnet server. Type
nano /etc/rc.local
to edit the file in nano. Add this line between the
"echo 30000...." and the "exit 0" lines:
/home/root/busybox telnetd -p 23 -l /bin/login &
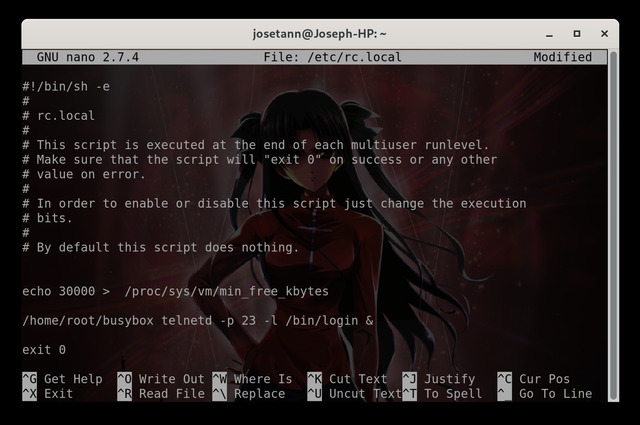
Now CTRL-X to exit, type Y when asked to save, and enter to keep the filename
(standard nano procedure if you're familiar). Now type the "reboot" command and
have your fingers crossed. Don't be too
alarmed if it doesn't boot all the way up right away, every so often it just
wants to do an fsck, and you'll freak out when it does thinking it's because
of some changes you did. If it doesn't boot up completely after ~5 minutes,
then start troubleshooting (check to see if it's stuck at uboot prompt again).
Once booted, ping to make sure it's online (if not responding, check and see
if it got a different ip address, you probably want to set a static ip at some
point), then telnet in; it should work (if not, you need to connect via serial
and run the command to start the telnetd server, now login via telnet and see
if you perhaps typed the command in /etc/rc.local incorrectly).
Once you verified that it boots correctly and automatically starts the telnet
server, I like to completely disconnect the serial port from the Doppler,
unplug it, wait 30 seconds and plug it back in. This ensures that EVERYTHING
was done properly and there's no gotchas. Again, it's possible that the boot
might take longer than usual, don't freak out until you've given it at least
five minutes (or more).
Now let's get the ssh server going. First, we download dropbear from
here
using this command on the doppler:
curl -o dropbearmulti http://www.thetechguide.com/files/doppler/dropbearmulti
Now, as before let's set the executable bit:
chmod 755 dropbearmulti
This time we'll copy it to /usr/sbin
cp dropbearmulti /usr/sbin/
Make sure it still has the executable bit set:
chmod 755 /usr/sbin/dropbearmulti
We now need to make some symlinks to dropbearmulti (much as busybox does).
ln -s /usr/sbin/dropbearmulti /usr/sbin/dropbear
ln -s /usr/sbin/dropbearmulti /usr/sbin/dropbearconvert
ln -s /usr/sbin/dropbearmulti /usr/sbin/dropbearkey
Before we can start the dropbear server, we need to generate some keys. Run
these three commands:
mkdir /etc/dropbear
dropbearkey -t rsa -f /etc/dropbear/dropbear_rsa_host_key
dropbearkey -t ecdsa -f /etc/dropbear/dropbear_ecdsa_host_key
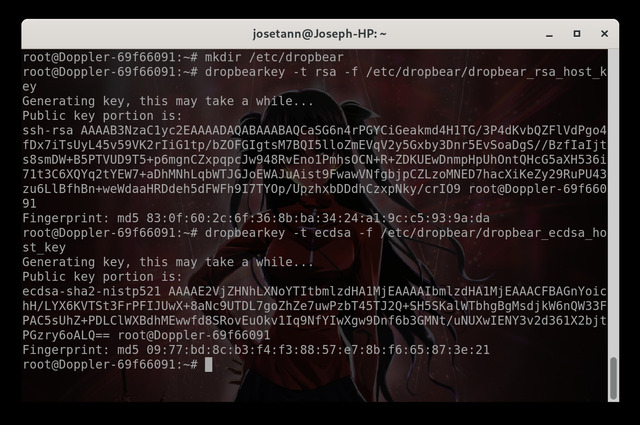
Note that if you're also writing a howto, delete that key then rerun the
dropbearkey command after you take a screenshot, so you don't give would-be
hackers sensitive info. Now start the dropbear server:
/usr/sbin/dropbear
You should be able to connect to the ssh server (make sure that you connect as
root and not your current user, on Debian 13 my command is
"ssh 192.168.1.62 -l root" to login to the Doppler with ip 192.168.1.62 as
the root user).
Assuming all works well, we can add the line to start the dropbear server in
/etc/rc.local like so:
nano /etc/rc.local
Add this right after your telnetd line:
/usr/sbin/dropbear &
Should look something like this:
Make sure to save (CTRL-X, then Y, then enter). Reboot the Doppler (can just
type the reboot command in the terminal), and verify that both telnet and
ssh logins work. Now you can feel free to mess with one OR the other, only
one at a time in case it breaks (thus you have the other as a backup).
Notes: This is currently on version 1214 on the Doppler. Very rough howto, may
have serious obvious mistakes. Nothing here should leave it in an unbootable
mode, but no guarantees, these are early days. Please don't pass around the url
for the howto while this message exists; I want to see a few others follow the
directions and make necessary changes before releasing it into the wild.
Questions? Ask in the
forum or
email me.
For the Privacy Policy, click
here. | |
| |
 |